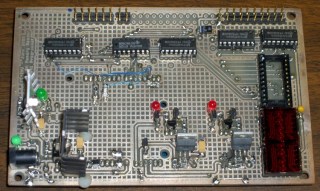
While I was putting together the Tek 492 memory board reader, I though it’d be a nice idea to add a small display. While the Arduino has USB serial I/O, the update rate is fairly pokey and an on-board display can provide more-or-less real time status.
Given that the reader was built for an early-80s memory board, I just had to use a pair of Litronix DL-1414 4-character LED displays from my parts heap. The DL-1414 datasheet [Update: link rot? try that] proudly proclaims:
The 0.112″ high characters of the DL1414T gives readability up to eight feet. The user can build a display that enhances readability over this distance by proper filter selection.
I think that distance is exceedingly optimistic.

However, I needed to see only a few feet to the benchtop. Even better, adding the displays required no additional hardware: the SPI-driven shift registers on the board already had address and data lines, plus a pair of unused bits for the write strobes. What’s not to like?
This schematic connects to the one you just clicked on; the two big blue bus lines are the same bus as in that schematic.
If you don’t have anything else riding the data bus, adding a pullup on the D7 bit that isn’t used by these displays will make all the bits float high; the DL-1414s seem to pull their inputs upward. That came in handy when I was debugging the EPROM-burning code, because reading data without an EPROM in the socket produced 0xff, just like an erased EPROM byte.
The two displays are the dark-red rectangle in the lower-right of the first picture, covered with a snippet of the Primary Red filter described there.
These closeups, without and with the filter, demonstrate why you really, really need a filter of some sort.


Using the displays is straightforward, given the hardware-assisted SPI code from there. You could actually do it with just the I/O pins on an Arduino board, but you wouldn’t be able to do anything else. If you don’t have any other SPI registers, you could get away with a pair of HC595 outputs: 7 data + 2 address + 2 strobes + 5 outputs left over for something else.
A few constants set the display size and a global buffer holds the characters:
#define LED_SIZE 4 // chars per LED #define LED_DISPLAYS 2 // number of displays #define LED_CHARS (LED_DISPLAYS * LED_SIZE) char LEDCharBuffer[LED_CHARS + 1]; // raw char buffer, can be used as a string
A routine to exercise the LEDs by scrolling all 64 characters they can display goes a little something like this:
Serial.println("Exercising LED display ...");
Outbound.Controls |= CB_N_WRLED1_MASK | CB_N_WRLED0_MASK; // set write strobes high
digitalWrite(PIN_DISABLE_DO,LOW); // enable data outputs
while (digitalRead(PIN_PB)) {
digitalWrite(PIN_HEARTBEAT,HIGH);
byte Character, Index;
for (Character = 0x20; Character < 0x60; ++Character) {
for (Index = 0; Index < LED_CHARS; ++Index) {
LEDCharBuffer[Index] = Character + Index;
}
UpdateLEDs(LEDCharBuffer);
delay(500);
if (!digitalRead(PIN_PB)) {
break;
}
}
digitalWrite(PIN_HEARTBEAT,LOW);
}
WaitButtonUp();
A routine to plop a string (up to 8 characters!) on the LEDs looks like this:
void UpdateLEDs(char *pString) {
byte Index = 0;
while (*pString && (Index < LED_CHARS)) {
Outbound.DataOut = *pString; // low 6 bits used by displays
Outbound.Address = ~Index; // low 2 bits used by displays, invert direction
Outbound.Controls &= ~(Index < LED_SIZE ? CB_N_WRLED1_MASK : CB_N_WRLED0_MASK);
RunShiftRegister();
digitalWrite(PIN_DISABLE_DO,LOW); // show the data!
Outbound.Controls |= CB_N_WRLED1_MASK | CB_N_WRLED0_MASK;
RunShiftRegister();
digitalWrite(PIN_DISABLE_DO,HIGH); // release the buffers
++pString;
++Index;
}
You can use sprintf() to put whatever you like in that string:
void ShowStatus(word Address,byte Data) {
sprintf(LEDCharBuffer,"%04X %02X",Address,Data);
UpdateLEDs(LEDCharBuffer);
}
Not, of course, that anybody would actually use DL-1414 displays in this day & age, but the general idea might come in handy for something more, mmmm, elegant…






